Azure Key Vault is an ideal place to securely store, manage, and retrieve secrets used by your application or service.
A secret is a name/value pair in which the value is any string or serialized object of length up to 25k bytes. We retrieve a secret's value by its name. Secret values are encrypted by default.
In this article, I will show how to add a secret to a Key Vault.
Navigate to the Azure Portal, sign in, and open the Azure Key Vault. If you do not have a Key Vault, see this article, for instructions on how to create one.
https://portal.azure.com
/creating-an-azure-key-vault
The Key Vault "Overview" blade displays, as shown in Fig. 1
Click the [Secrets] button (Fig. 2) in the left menu to display the "Secrets" blade, as shown in Fig. 3
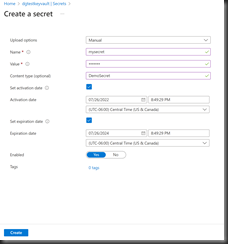
On the "Secrets" blade, click the [Generate/Import] button (Fig. 4) to display the "Create a secret" dialog, as shown in Fig. 5.
At the "Uploads" dropdown, select "Manual".
At the "Name" field, enter a name for your secret.
At the "Value" field, enter the value of your secret. This can be any string. It will not display as you type.
Optionally, you can select a range in which the secret is valid. To do so, select either or both of the checkboxes ("Set activation date" and "End activation date"). Fields will display, allowing you to enter the date, time, and time zone for the earliest and/or latest time that the secret can be accessed.
If you do not want to make the secret available yet, but have not yet decided on which date it will be available, you can toggle the "Enabled" switch to "No" and change it to "Yes" when you decide the secret should be available.
If you wish, you can add one or more tags to the secret. Tags are name/value pairs that provide metadata for an Azure resource. They don’t affect the resource, but they can be useful when grouping them together on reports – for determining which resources belong to which departments, for example.
After completing this dialog, click the [Create] button (Fig. 6) to add the Secret to the Key Vault. The "Secrets" blade will display again with the newly-added secret listed, as shown in Fig. 7.
You can now use this secret in code or in a variety of Azure services.