Granting Azure Active Directory Permissions to an App Registration
October 28, 2022 2:07 Comments [0]In a previous article, I showed you how to create an Active Directory user account.
Accounts are not much use unless they can do something, such as create, read, update, or delete objects. In order for a user account to do anything, that account must have permissions to perform the attempted action. A user can grant permissions to some objects associated with themselves. For example, I may give you permission to read my calendar; but, for most objects and actions, an AD Administrator is responsible for granting those permissions. Here are the steps to take while logged into Azure as an AD Administrator for the subscription involved. This article describes how to grant access to add permission to read user accounts (which can be done via Microsoft Graph), but the steps are similar regardless what permissions you are granting.
Log into the Azure Portal as an Administrator and search for Azure Active Directory, as shown in Fig. 1 to display the Azure Active Directory "Overview" blade, as shown in Fig. 2.
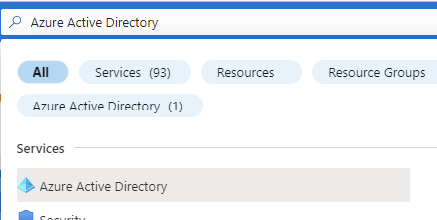
Fig. 1
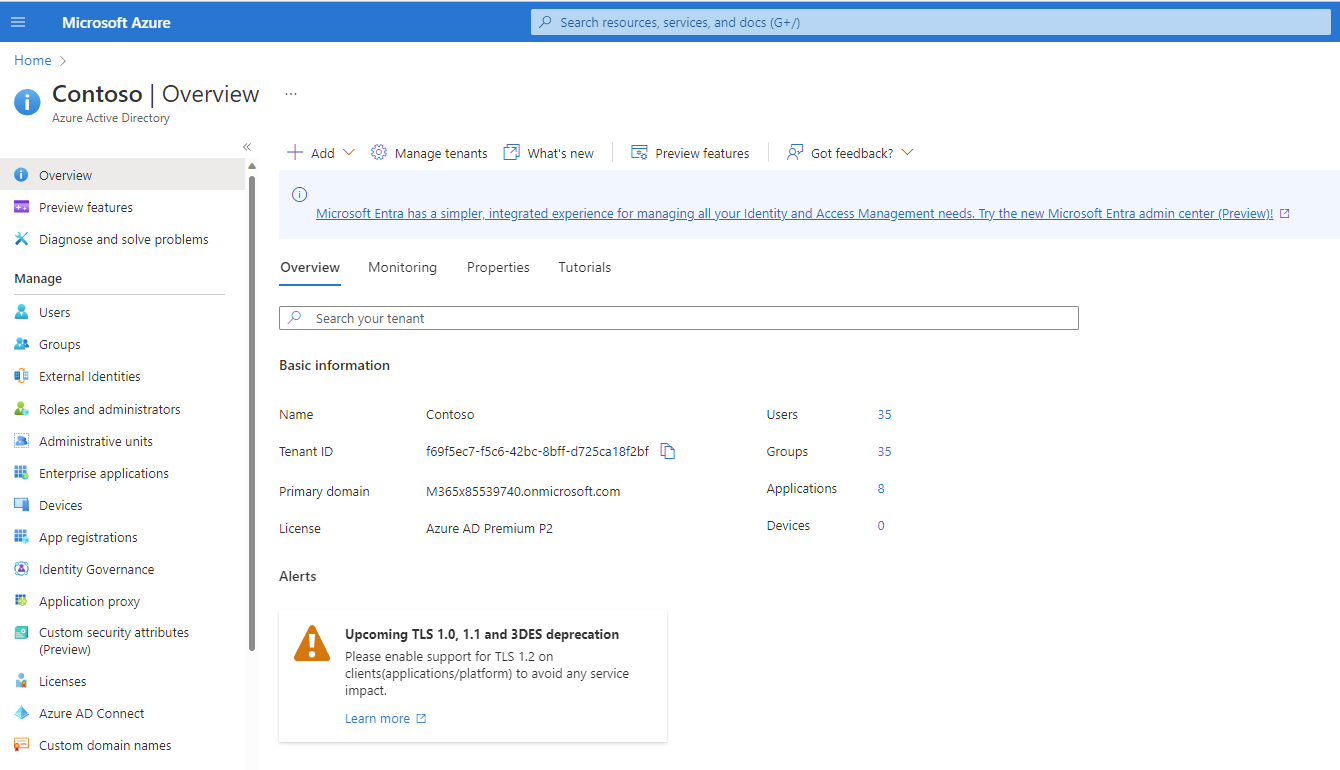
Fig. 2
Click the [App registrations] button (Fig. 3) to open the "App Registrations" blade, as shown in Fig. 4.
Fig. 3
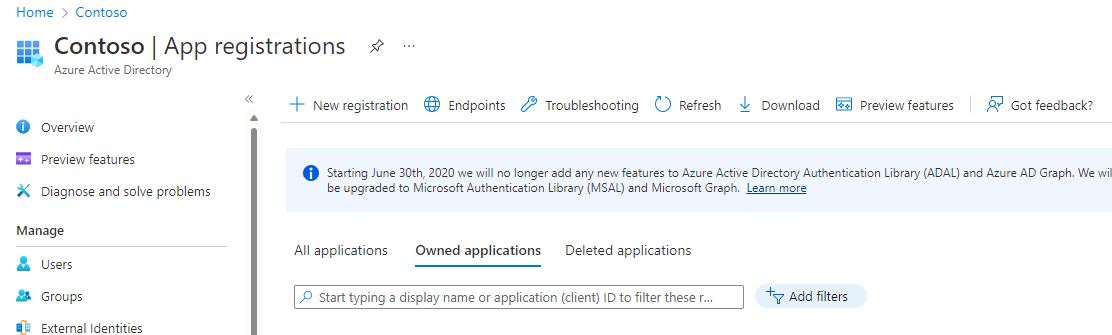
Fig. 4
Select your App registration to open its details page, as shown in Fig. 5.
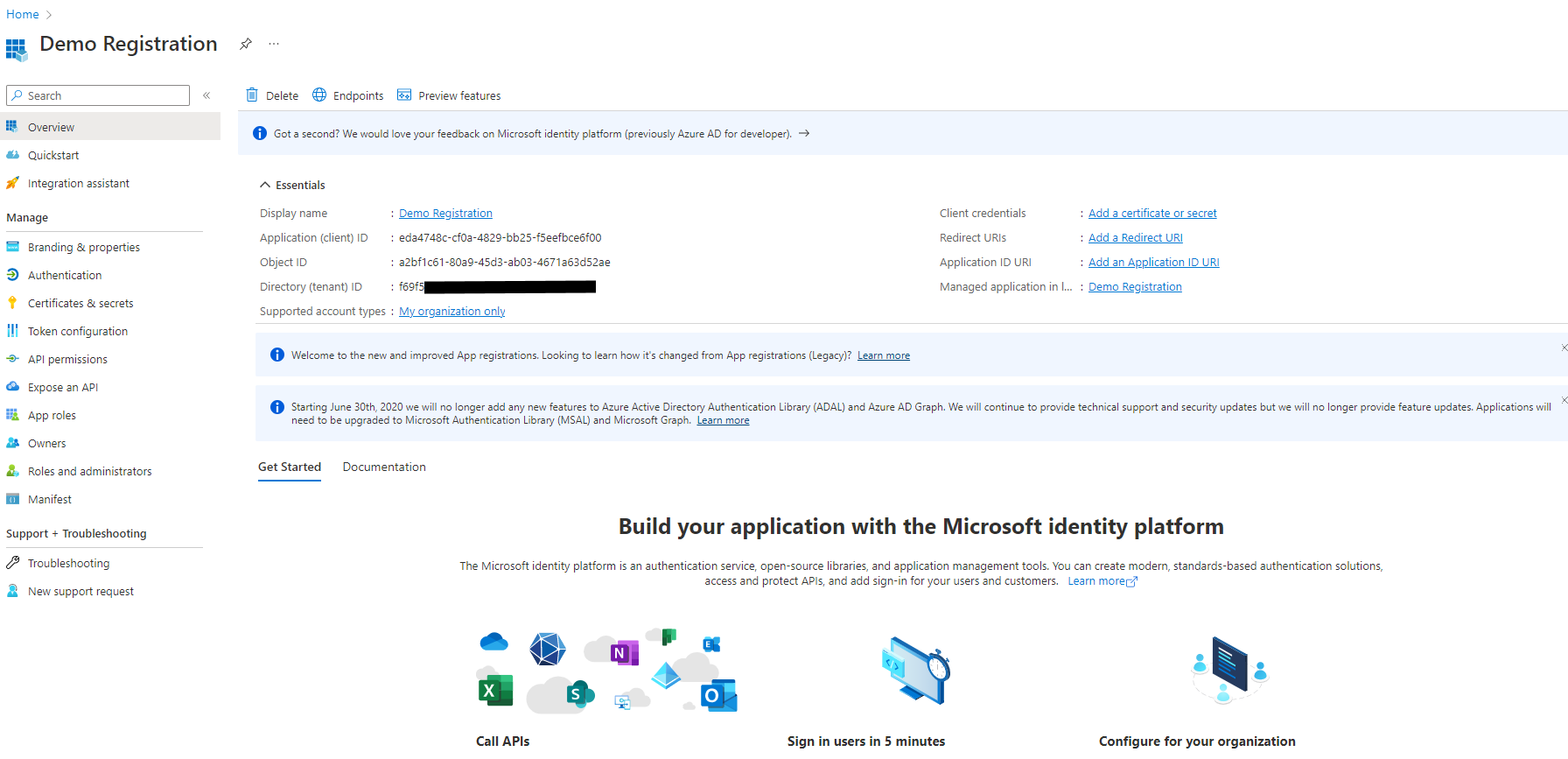
Fig. 5
Click the [API permissions] button (Fig. 6) in the left menu to display the "API permissions" blade, as shown in Fig. 7.
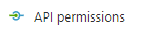
Fig. 6
Fig. 7
Click the [Add a permission] button (Fig. 8) to display the "Request API permissions" dialogue, as shown in Fig. 9.
Fig. 8
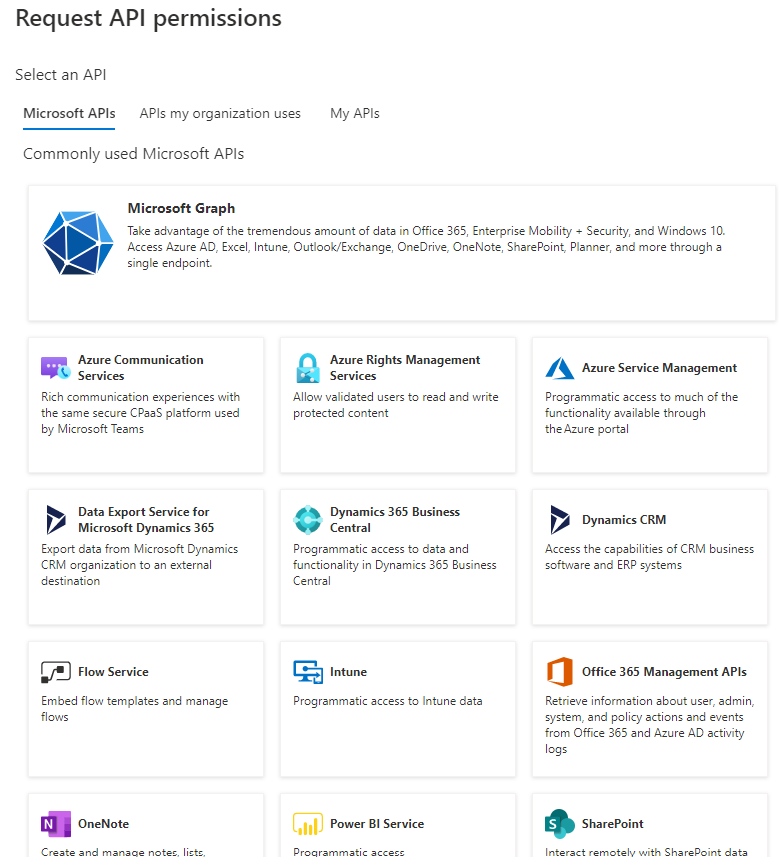
Fig. 9
Click the "Microsoft Graph" button (Fig. 10) to filter the permission request to Microsoft Graph permission types, as shown in Fig. 11.
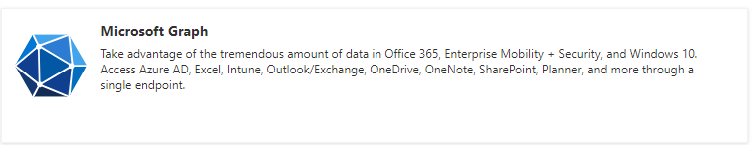
Fig. 10
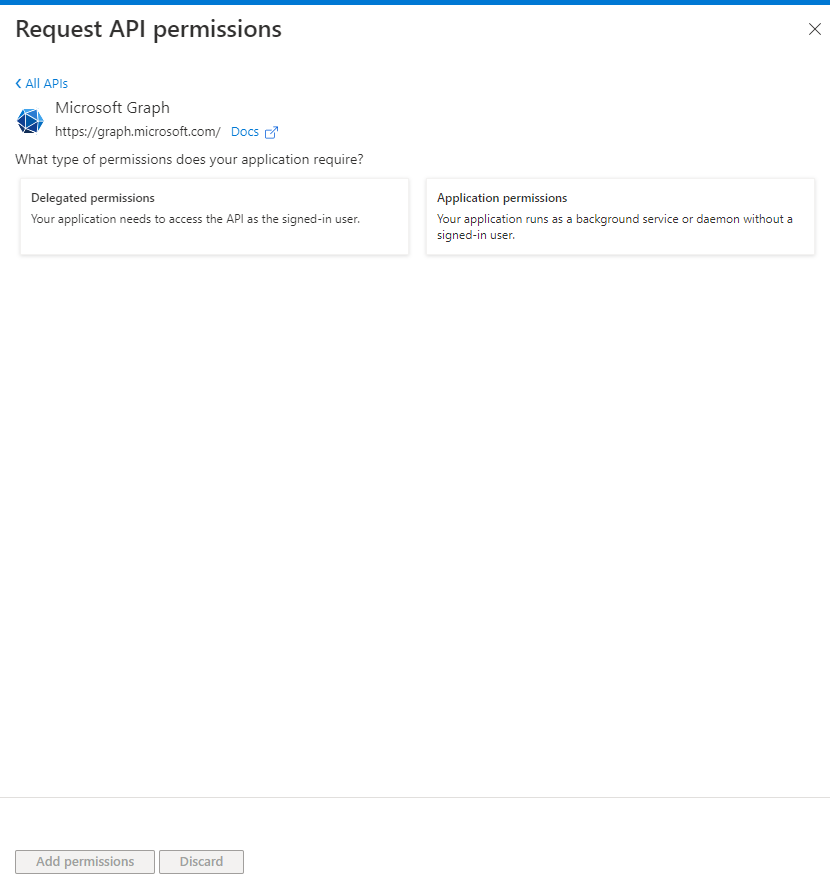
Fig. 11
Click the [Application permissions] button (Fig. 12). This allows the account to make calls, even if it is not explicitly signed in to AD. A list of permission categories displays, as shown in Fig. 13.
Fig. 12
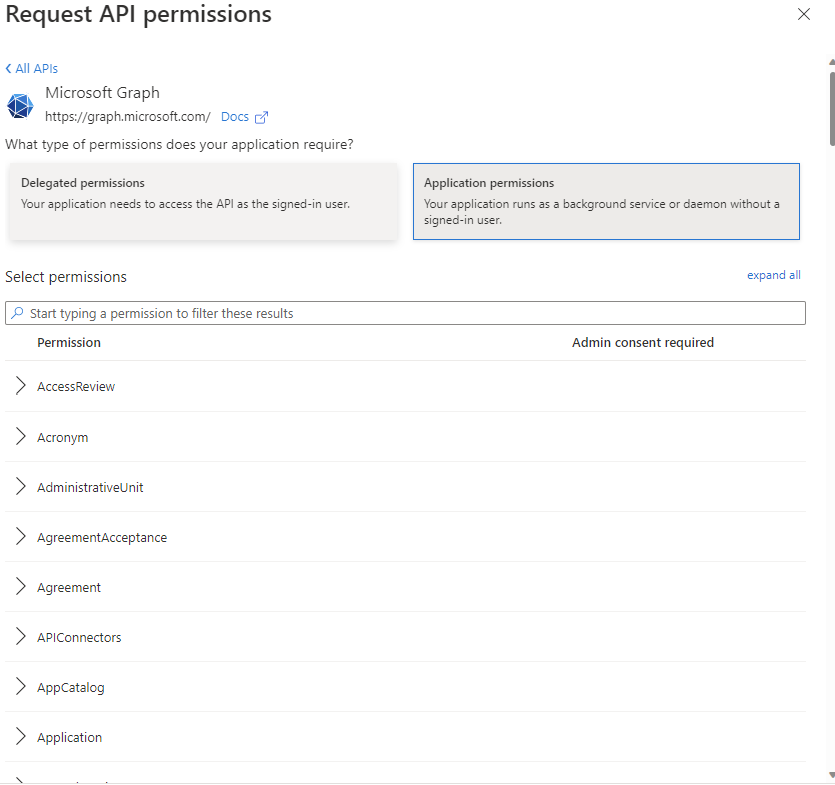
Fig. 13
Here you can expand a category and select the permissions to grant to an account via this Application Registration. Fig. 14 shows the "User" category expanded with the "User.ReadAll" selected, which would allow an account to Read all users' information in the Active Directory, but would not allow them to change, add, or delete user information.
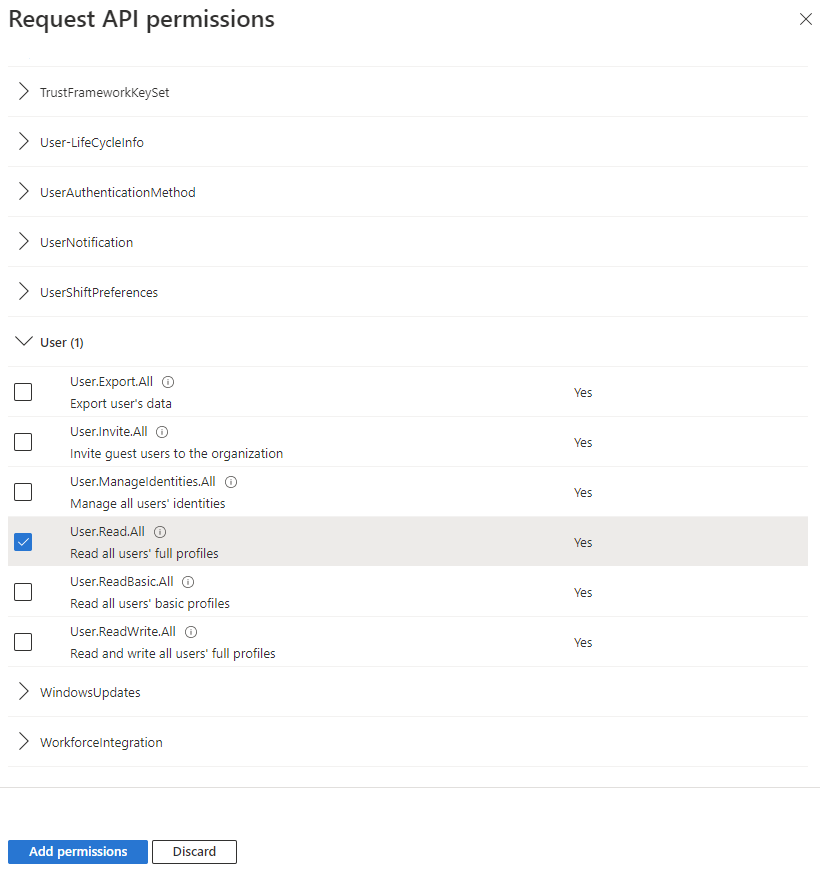
Fig. 14
Click the [Add permissions] button (Fig. 15) to save selected permission changes.

Fig. 15
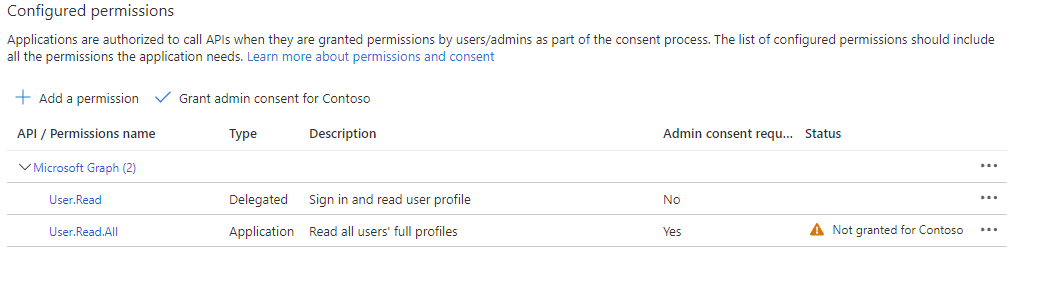
Fig. 16
The Configured Permissions list displays again with the _User.Read.All_ application permission added. Note the "Yes" under the "Admin consent required column" and the "Not granted" warning in the "Status" column. This indicates that the permission will not take effect until an admin consents to it. Not all permissions require this, but _User.Read.All_ does. Click the [Grant admin consent" button (Fig. 17) and click the [Yes] button when prompted for confirmation (Fig. 18).
Fig. 17 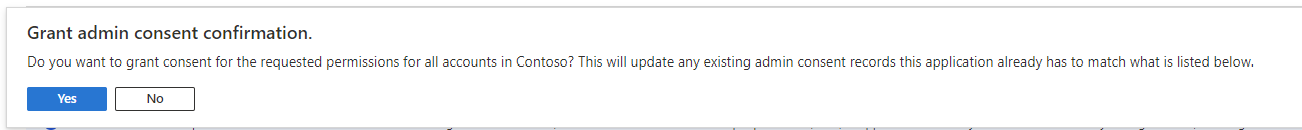
Fig. 18
The Configured Permissions list displays again with the warning replaced by a "Granted" message in the "Status" column, as shown in Fig. 19. The account now has permission to read user information.
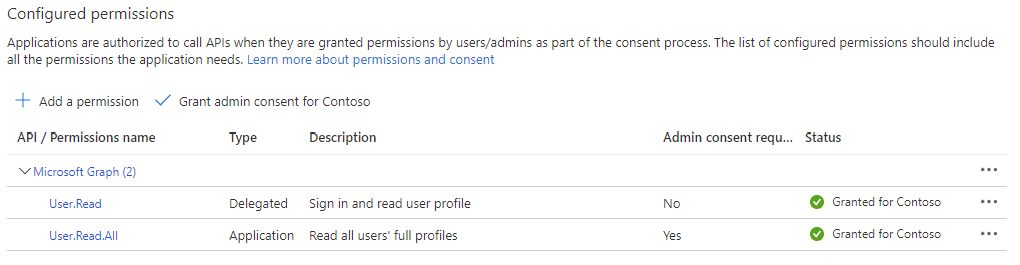
Fig. 19
As you can see, the steps for granting permissions to an Active Directory User Account are simple. The catch is that you must be logged on as the owner of the object acted upon or as an AD Administrator in order to grant these permissions.